Why 2026 Changes the Cybersecurity Conversation for Nonprofits
Nonprofit and faith-based leaders face a different set of expectations regarding technology risk than they did even a few years ago. Cybersecurity is no longer a topic reserved for large enterprises with dedicated IT departments. It now affects organizations of every size, including those led by small teams, volunteers, or part-time administrators.
Donors expect their information to stay protected. Boards expect leadership to manage risk responsibly. Insurance providers increasingly ask detailed questions about security controls and recovery plans. Regulators continue to raise standards around data handling and privacy. None of this reflects a lack of trust in nonprofits, but rather how much trust nonprofits are given every day.
The good news is that readiness does not require enterprise-level tools or a complete technology overhaul. It requires clarity, structure, and realistic priorities. Nonprofit cybersecurity is less about reacting to fear and more about making thoughtful decisions that support stewardship, accountability, and mission continuity. When approached with intention, cybersecurity becomes another way to protect the people and communities you serve.

What Cybersecurity Really Means for Nonprofits Now
Cybersecurity can sound abstract or overly technical, which makes it easy to postpone. In reality, cybersecurity for nonprofits focuses on a few practical areas that already affect daily operations.
According to the 2025 Nonprofit Cybersecurity Incident Report from Community IT Innovators, nonprofit organizations across the United States saw nearly 500 suspected account compromises, illustrating how frequently attackers attempt to exploit vulnerable systems and access credentials without authorization.
First, it means protecting donor, member, and financial data. This includes online giving platforms, accounting systems, donor databases, and payroll tools. These systems hold information that people trust you to safeguard.
Second, it means securing the email and cloud platforms your team uses every day. Email remains the most common entry point for cyber incidents. Cloud tools like Microsoft 365 or Google Workspace are powerful, but only when access and settings receive proper attention.
Third, cybersecurity involves managing how staff and volunteers access systems. Many nonprofits rely on shared responsibilities, rotating volunteers, or seasonal staff. Without clear access controls, accounts often remain active longer than intended, increasing risk.
Finally, cybersecurity supports your ability to continue operating after a disruption. This includes having reliable backups, clear response steps, and confidence that you can keep serving your community even when systems fail.
Cybersecurity is not only about stopping incidents. It is about limiting damage, restoring operations, and preserving trust when problems occur. That perspective matters for nonprofit leaders who care deeply about credibility and continuity.

The Most Common Cybersecurity Gaps
Across nonprofits and churches, certain cybersecurity gaps appear again and again. These gaps rarely stem from neglect. They usually come from limited time, limited staffing, and the pressure to keep programs running. Below are the most common ones:
1. Shared or Unmanaged Logins
Teams sometimes share email accounts or system credentials for convenience. Over time, it becomes unclear who has access to which systems and for what purpose. This lack of clarity increases the risk of unauthorized access and makes it harder to trace activity when something goes wrong.
2. Inconsistent Use of Multi-Factor Authentication
Some systems require multi-factor authentication, while others do not. In many cases, enforcement varies by role or user. This inconsistency leaves critical accounts exposed, especially email and financial systems that attackers commonly target.
3. Former Staff or Volunteers Retaining Access
Access often remains active long after a role ends. Without a clear offboarding process, former staff members or volunteers may still reach cloud platforms, shared files, or third-party tools. These lingering accounts create unnecessary risk and complicate accountability.
4. Backups That Are Untested or Poorly Protected
Many nonprofits have backups in place, but few test them regularly or protect them from ransomware. A backup that cannot be restored quickly or has been compromised does not support recovery when it matters most.
5. No Documented Incident or Continuity Plan
When an incident occurs, leaders often scramble to determine who should respond, which vendors to contact, and how to communicate with staff, donors, or board members. Without documented guidance, response time slows and confusion increases.
These gaps carry real consequences. Insurance providers may delay or deny coverage. Donors may question how their information was handled. Operations may slow or stop during recovery. Addressing these issues before they cause disruption protects both reputation and service delivery.

A Readiness Framework for Nonprofit Cybersecurity
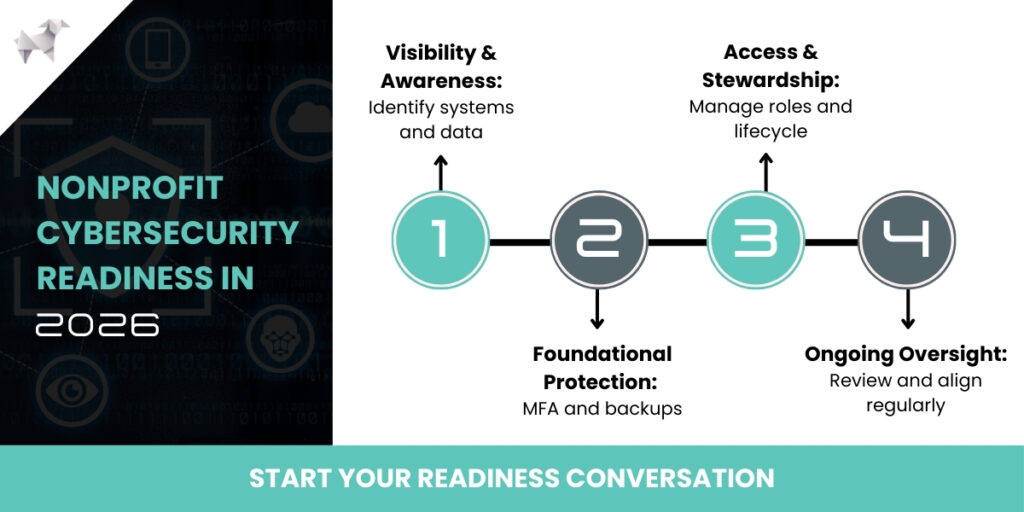
Contrary to common assumptions, preparing for nonprofit cybersecurity does not require perfection; it requires progress. Here’s a phased approach that helps leaders focus on what matters most without overwhelming teams or volunteers.
Phase 1: Visibility and Awareness
Readiness starts with understanding what you have. This phase focuses on clarity rather than control.
Begin by identifying your core systems. List email platforms, donor databases, accounting tools, file storage, and any systems that hold sensitive information. Next, review who has access to each system and why.
It also helps to understand where sensitive data lives. Donor information, payment details, and personal records often exist across multiple platforms. Knowing where that data resides allows you to protect it more effectively.
This phase does not require advanced tools. It requires documentation, discussion, and leadership attention. Visibility sets the foundation for every improvement that follows.
Phase 2: Foundational Protections
Once visibility improves, foundational protections come next. These steps reduce risk significantly without adding heavy complexity.
Multi-factor authentication should protect all critical systems, especially email, cloud platforms, and financial tools. This single step blocks many common attacks.
Secure backups support recovery. Backups should run regularly, store data separately from production systems, and undergo testing to confirm they work when needed.
Email and cloud security settings deserve attention as well. Basic protections like spam filtering, account alerts, and secure sharing policies strengthen daily operations.
These measures align closely with insurance requirements and nonprofit IT risk management best practices. They also deliver high value without heavy cost.
Phase 3: Access and Stewardship Controls
This phase focuses on responsible access. It reflects the stewardship values many nonprofits already practice in other areas.
Role-based access ensures people only reach the systems they need to do their work. This reduces accidental exposure and limits the impact of compromised accounts.
Clear onboarding and offboarding processes help teams manage change. When staff or volunteers join, access gets granted intentionally. When roles end, access gets removed promptly.
Documentation supports continuity. Written procedures allow leadership transitions, board oversight, and smoother responses during incidents.
These controls strengthen nonprofit data security while respecting the realities of volunteer-driven environments.
Phase 4: Ongoing Oversight Without Internal Burden
Cybersecurity does not stop after setup. Systems change, staff roles evolve, and risks shift.
Ongoing oversight includes regular reviews of access, backups, and security settings. It also includes aligning cybersecurity efforts with continuity planning and insurance requirements.
Many organizations benefit from advisory support during this phase. Nonprofit managed services delivered through an advisory lens help leaders stay aligned without adding operational stress.
Progress matters more than perfection. Consistent review builds confidence over time.
Cyber Insurance, Continuity, and Why They Are Now Connected
Cyber insurance plays a growing role in nonprofit risk planning. Insurers now look closely at cybersecurity controls before offering coverage or renewing policies.
This shift exists because incidents have become more disruptive and more expensive. Insurers want confidence that organizations can prevent common threats and recover responsibly.
Continuity planning supports both recovery and coverage. When nonprofits demonstrate they can restore systems, communicate clearly, and continue serving communities, insurers respond more favorably.
Without preparedness, organizations risk coverage gaps, delayed claims, or higher premiums. More importantly, they risk losing the ability to operate during critical moments.
Cybersecurity supports mission continuity. It helps ensure services remain available during disruption, especially for churches and nonprofits serving vulnerable populations.
Church cybersecurity deserves special attention in this conversation. Faith-based organizations often manage sensitive pastoral information, donor records, and community communications. Protecting that trust matters deeply to congregations and leadership alike.

Why Advisory-Led Managed Services Make Sense for Nonprofits
Many nonprofits struggle with the idea of outsourcing technology decisions. They value ownership and accountability. Advisory-led nonprofit managed services respect that perspective.
An advisory approach focuses on guidance rather than control. Leaders retain decision-making authority while gaining clarity on priorities, risks, and options. Right-sized controls align with mission and budget. Instead of pushing tools, advisors help organizations choose what fits their structure and goals.
This model also reduces internal workload. Staff and volunteers receive support without carrying the full burden of oversight and maintenance. As tools, threats, and expectations change, advisory partnerships provide continuity. They help nonprofits adapt without starting over each year.
Lamb Telecom operates in this advisory space, supporting nonprofits and faith-based organizations with technology planning, risk conversations, and continuity alignment. The focus remains on stewardship, clarity, and practical outcomes rather than managing every technical detail.

Strengthening Trust and Mission Continuity
Nonprofit cybersecurity does not need to feel overwhelming. It starts with awareness, builds through practical steps, and grows with consistent oversight. Each improvement strengthens the foundation beneath your mission.
As expectations rise, 2026 offers an opportunity to prepare with purpose rather than react to incidents. A readiness conversation can clarify where you stand and where to focus next.
If you want to assess your current posture, consider scheduling a nonprofit cybersecurity readiness review or seeking a second opinion on your security and continuity setup. Preparation begins with understanding, and understanding builds confidence.

